We’ve shipped VulnerableCode v30 with many improvements to help you find FOSS vulnerabilities, and improve overall FOSS security:
Publicly available, with brand new web UI and API access
VulnerableCode is now publicly available, as a free and open database of open source software package vulnerabilities. VulnerableCode.io provides a comprehensive UI, a REST API and a database for the VulnerableCode project.
The newly enhanced web UI for VulnerableCode makes it easier for all users to search and find packages and vulnerabilities. Users of other AboutCode projects will appreciate the similarity with other projects like ScanCode.io.
Please note that VulnerableCode v30.0.0 is not backward-compatible.
We broke everything getting to this release, including refactoring the core processing. Because of these extensive changes, it is not possible to migrate existing imported data to the new schema. Instead, you will need to restart imports from an empty database (we provide a database dump) or access the public.vulnerablecode.io live instance.
Software package focused, built for the FOSS community
VulnerableCode focuses on software packages first, using a Package URL (PURL) as the key and natural identifier for packages; this makes it easier to find a package and whether it is vulnerable.
The VulnerableCode project is a FOSS community resource to help improve the security of the open source software ecosystem and its users at large.We also added a CC-BY-SA-4.0 license for VulnerableCode data, as this is the highest common denominator license among all the data sources we collect and aggregate (#277).
Improved data collection, with expanded data sources and enhanced package endpoints
v30.0.0 includes several updates to enhance the aggregation, correlation, and curation of software component vulnerability data from multiple sources.
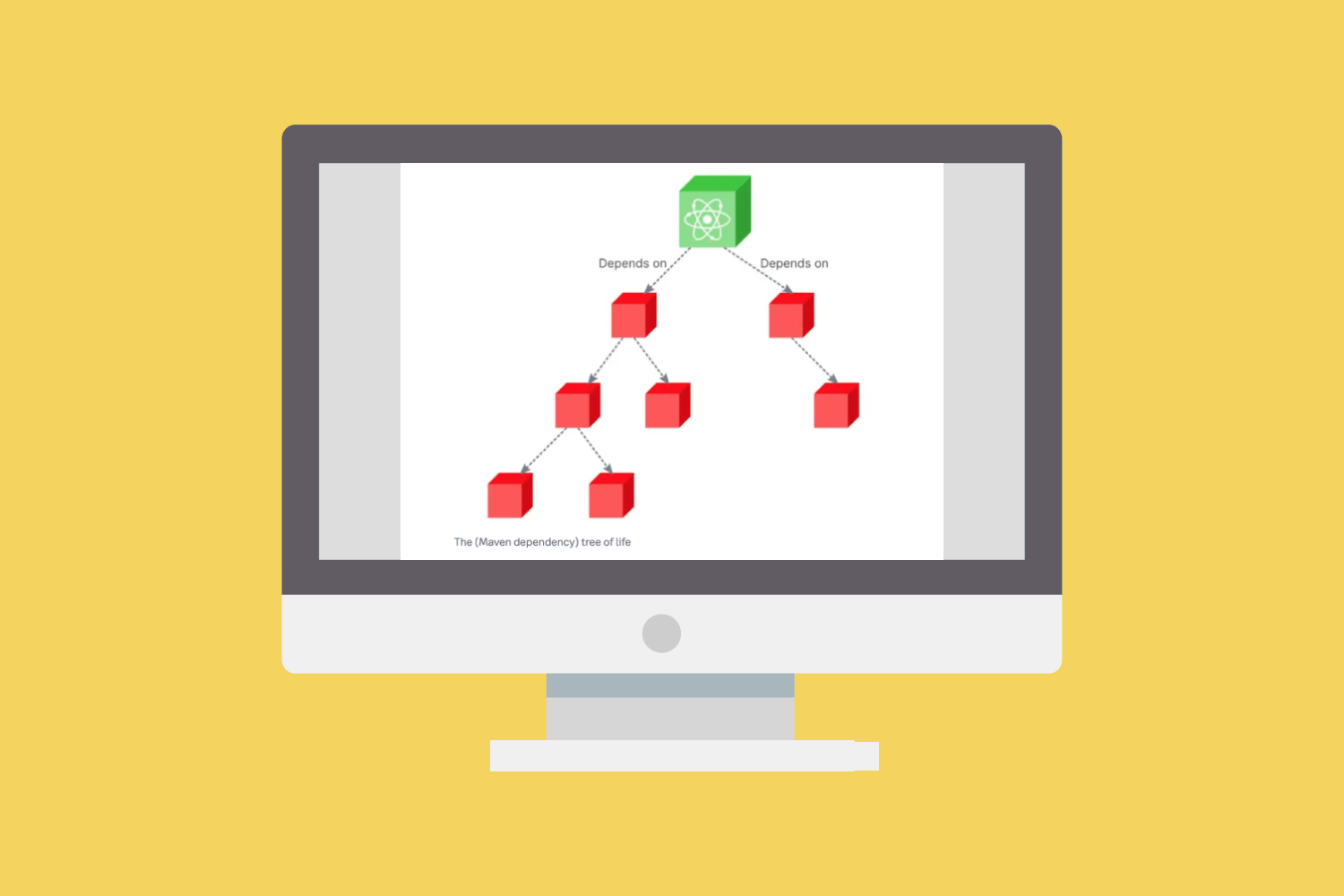
Data collection in VulnerableCode now works in two steps:
- An
importeringests data from a specific data source. - An
improverthen transforms and converts the imported data into standard vulnerability and package fields in the VulnerableCode database. Animproveralso refines and enriches imported and existing data, using external data sources (#361).
As part of refactoring the core processing (#597), we migrated existing importers, including NGINX, GitHub, Alpine, NVD, OpenSSL, and RedHat, to the new structure, and added new importers, including GitLab, PostgreSQL, PyPi, and PYSEC. The AboutCode community will continue to add new importers and improvers for more sources in future releases.
Several other improvements enhance VulnerableCode’s search functionality, including:
- Find vulnerabilities across different data sources, including affected packages and fixed packages (that fix a vulnerability), and across package version ranges (#149, #869, #140)
- Add bulk search support for CPEs (#844)
- Include additional filters for vulnerability’s endpoints return fixed packages that match queries of type, name, namespace, subpath, and qualifiers (#140, #784)
Changelog
For more information on all of the updates in VulnerableCode v30.0.0, please see the changelog on GitHub.
Run VulnerableCode
Visit public.vulnerablecode.io for direct UI access.
Read the docs on how to install VulnerableCode locally.
We recommend running VulnerableCode with Docker to guarantee the availability of all features with the minimum configuration required, but you can also install VulnerableCode locally as a development server with some limitations.
Want to learn more? Watch this video with nexB co-founder and CTO Philippe Ombredanne explaining VulnerableCode along with a technical deep dive.